What Is a TPM?
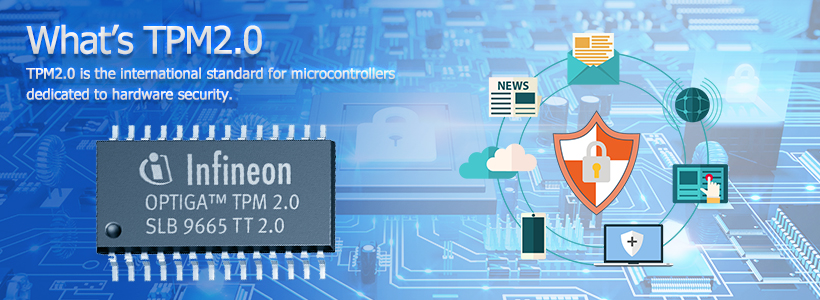
A Trusted Platform Module (TPM) is a specialized hardware chip designed to enhance computer security. It provides a secure environment for storing sensitive data, such as encryption keys and passwords. This article will explain what a TPM is, why it is important, and how it functions within a computer system.
What Is a TPM and How Does It Work?
A TPM is a physical security device embedded into a computer's motherboard. It performs cryptographic operations and securely stores encryption keys, passwords, and digital certificates. The TPM works alongside the operating system to protect sensitive data from unauthorized access, malware, and other security threats.
The Role of TPM in Security
The primary function of a TPM is to safeguard sensitive information. It provides hardware-based protection against attacks that software alone cannot prevent. The TPM uses a combination of encryption and secure key storage to make it extremely difficult for hackers to steal data, even if they have physical access to the computer.
In addition, the TPM can perform operations like encrypting and signing data, verifying the integrity of system files, and enabling secure boot processes. This ensures that the system only runs trusted software, preventing malware from loading during startup.
Key Features of a TPM
TPMs have several key features that make them an essential component for modern computer security. These include:
• Secure Key Storage: The TPM securely stores encryption keys, which are used to protect sensitive data. These keys are never exposed to the outside world, making it very difficult for hackers to access them.
• Data Encryption: TPMs support hardware-based encryption, which is more secure and efficient than software-based encryption methods.
• Platform Integrity Checking: The TPM can verify the integrity of the operating system and hardware during startup. This helps prevent malware from altering the system before it boots.
• Authentication: TPMs can be used for two-factor authentication (2FA) and other security features. For example, they can store biometric data or PINs for user authentication.
Why Is TPM Important?
TPMs are important for several reasons. As cyber threats become more sophisticated, it is essential to have hardware-based security to protect sensitive data. Here's why TPMs are necessary for modern computers:
Improved Data Protection
With increasing data breaches and cyberattacks, protecting personal and business data has never been more critical. A TPM adds an extra layer of security that is difficult to bypass. By storing encryption keys in a hardware device, the TPM ensures that even if a hacker gains access to the system, they cannot easily access the protected data.
Protection Against Malware and Ransomware
Malware and ransomware attacks have become a major concern for users and organizations. These malicious programs can steal or lock data, causing significant damage. TPMs help prevent such attacks by ensuring that the system only runs trusted software. If malware tries to modify the system, the TPM can block it, preventing the attack from taking place.
Meeting Compliance Standards
In industries such as finance, healthcare, and government, strict regulations govern the protection of sensitive data. TPMs help businesses meet these compliance requirements by providing hardware-based security that is recognized by regulatory authorities. Using TPMs ensures that organizations can protect customer data and maintain compliance with industry standards.
TPM in Windows 11
Windows 11 has raised the minimum system requirements for secure computing, and one of those requirements is the presence of a TPM 2.0 chip. This requirement ensures that users have access to the latest security features, such as BitLocker encryption and secure boot, which are essential for protecting personal and business data.
TPM 2.0 and Windows 11 Security
TPM 2.0 offers several enhancements over earlier versions of the TPM. It provides better encryption algorithms, improved key management, and support for modern security standards. With Windows 11, TPM 2.0 is required to enable features such as:
BitLocker Drive Encryption: BitLocker helps encrypt the entire hard drive, preventing unauthorized access to data. TPM 2.0 provides the secure storage of encryption keys, ensuring that the data remains protected.
Secure Boot: Secure boot verifies that the operating system and other essential software are trusted before they load. If an attacker tries to modify the boot process, TPM 2.0 can block the malware from loading.
Windows Hello: TPM 2.0 stores biometric data like fingerprints and facial recognition, enabling users to log in securely with Windows Hello.

Why Windows 11 Requires TPM 2.0
The requirement for TPM 2.0 in Windows 11 is part of Microsoft's effort to ensure higher levels of security for all users. By enforcing TPM 2.0, Microsoft ensures that new systems come equipped with the latest hardware-based security features. This helps protect users against evolving cyber threats.
How to Check if Your PC Has a TPM
If you're wondering whether your computer has a TPM chip, there are simple ways to check. Here's how you can check if your system supports TPM 2.0 on Windows 10 or Windows 11:
- •Press Win + R to open the Run dialog box.
- •Type tpm.msc and press Enter.
- •In the TPM Management window, look for the "Status" section. If the TPM is enabled, it will display "The TPM is ready for use."
- •If your system does not have TPM or if it’s not enabled, you may need to check your motherboard’s documentation or BIOS settings to enable it.
How to Enable TPM on Your PC
If you discover that your TPM is not enabled, you can easily turn it on via the BIOS/UEFI settings. Follow these steps:
- • Restart your computer and enter the BIOS/UEFI settings by pressing a specific key during startup (usually F2, DEL, or ESC).
- • Look for the TPM option in the security settings menu.
- • Enable TPM and save the changes before exiting the BIOS/UEFI.
- • Once enabled, your system will be ready to take full advantage of the security features provided by TPM.
Conclusion
A TPM is a critical component for securing your computer and personal data. It provides hardware-based protection against threats like malware, ransomware, and unauthorized access. As cybersecurity becomes more important, TPMs play a key role in keeping your system safe.
For Windows 11 users, having a TPM 2.0 chip is not just a requirement for installation but a fundamental part of securing the system. With increasing cyber threats, TPMs are no longer optional but a necessary feature for ensuring data protection and system integrity.
By enabling and utilizing a TPM, you are taking a significant step in protecting your personal and business information from malicious attacks.
